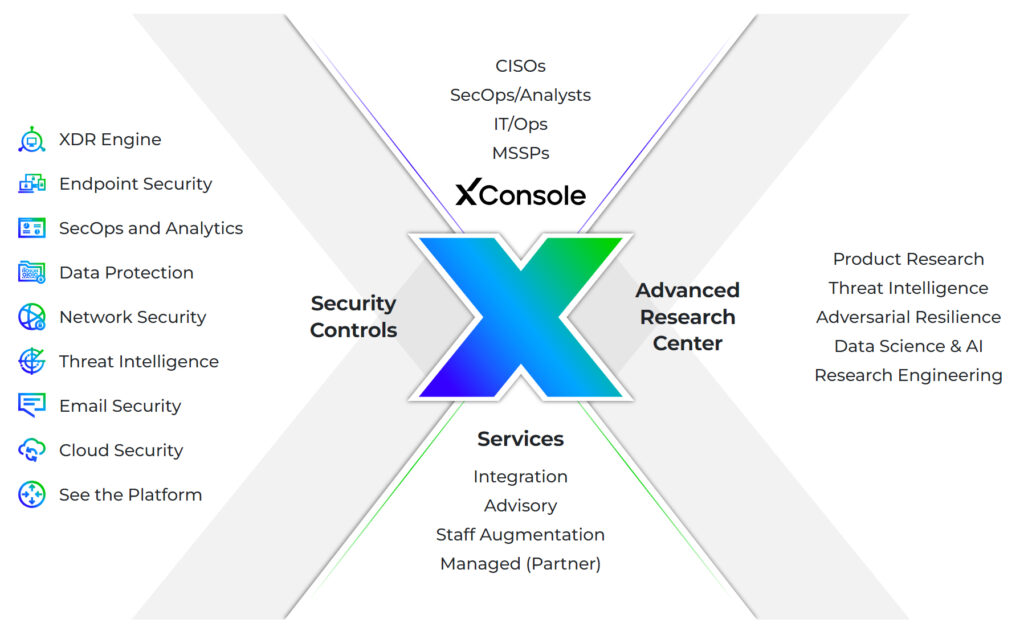
Trellix
A pioneer in defense against APT attacks
As a vanguard of the XDR revolution, Trellix prioritises threat prevention over attack detection. In a cyberwar situation, you need enhanced protection. Utilising an intelligent, adaptive ecosystem, you can anticipate and prevent attacks, identify root causes, and react in real-time. It is not by chance that Trellix has been detecting more than 50% of 0-day attacks for years.